Quantum Supremacy Will Not Break Your Encrypted Data Anytime Soon


- Quantum Supremacy - definition
- Encryptions remain uncrackable so far
- Peter Shor's Algorithm
- Final words
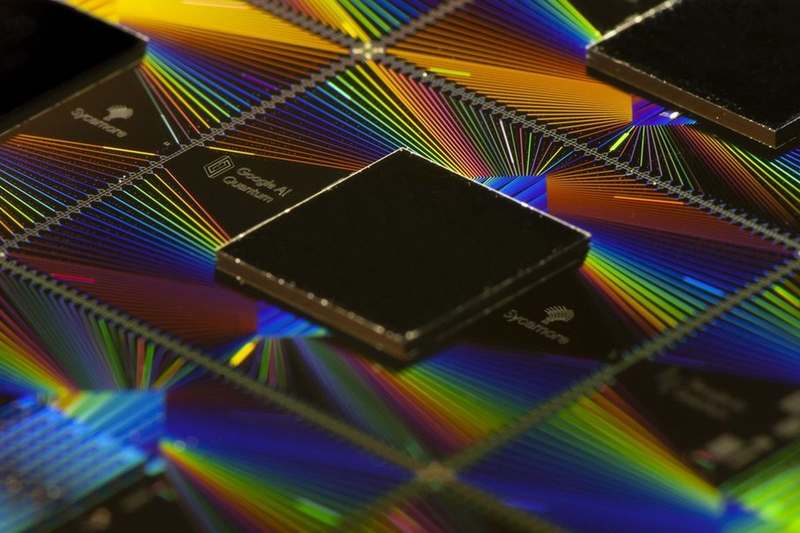
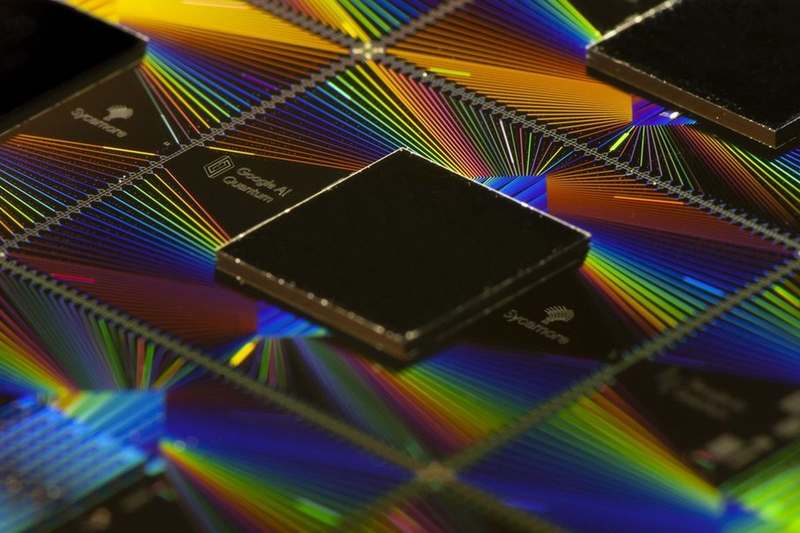
Google researchers completed an experiment that demonstrates the first computation that you can perform only with a quantum processor. It is something scientists call “quantum supremacy.” The quantum computer can perform tasks that no conventional processor can within a reasonable period.
If achieved, quantum supremacy would eventually change the world of cryptography forever. Deciphering a code would only take seconds or minutes instead of long years.
As a result, the current cyber encryption methods require an update. Otherwise, they won’t be able to withstand the immense computing power of a quantum processor.
The problem is that scientists and media people think differently. And no, Google’s quantum supremacy experiment will not put an end to the data encryption as we know it, at least not any time soon.
What Is Quantum Supremacy?
Quantum computing offers much higher speeds compared to regular computers when facing complex calculations. Traditional processors require months, even years, to solve complicated equations and problems. However, quantum computers can find solutions exponentially faster by using qubits.
According to the paper that Google published, their quantum processor “takes about 200 seconds to sample one instance of the quantum circuit one million times.” An existing supercomputer that uses classical computer architecture would need 10,000 years to complete a task of such complexity, the paper adds.
However, IBM was quick to rebuff Google’s claims that it reached quantum supremacy. On October 21, the company announced that its supercomputer “Summit” managed to complete the task in two and a half days. Therefore, the race is still on.
“We argue that an ideal simulation of the same task can be performed on a classical system in 2.5 days and with far greater fidelity.”
IBM’s Edwin Pednault, John Gunnels, and Jay Gambetta
What makes a quantum processor work so much faster than a classical one?
Traditional computers use zeroes and ones to store data in pieces we call bits. Meanwhile, quantum processors work at the atomic level and use quantum bits instead. We call them qubits, which use zeroes, ones, and any number in between. Thus, you get far greater efficiency when processing data.
If you think it is too complicated, think again. IBM released a commercial version of its 14th quantum computer in October. It had 53 qubits of computing power, nearly double the capacity of the earlier one they released a year ago.
Did you read any news reports that an evil government uses IBM’s quantum computer to crack codes? I bet you didn’t.
Quantum Supremacy Does Not Mean Unsafe Cryptography Codes
Quantum computers do not have any practical uses at this stage. Just because they are available for commercial practices does not mean you can use them for instant budgeting, for example. And they cannot crack cryptography codes as well.
What these computers can do is process large amounts of data in parallel, resulting in markedly shorter processing time. Traditional devices, on the other hand, process data sequentially. Classical machines have been successful in reproducing the performance of quantum computers of up to 40 qubits, until recently. Google’s Sycamore processor is using 53 qubits.
But further developments in quantum computing will require building a physical quantum computer. Both Google and IBM still haven’t been able to do that. And I doubt there is one hidden somewhere in a secret R&D laboratory.
But if such a computer is available, how could it break a code that would take current classical machines tens of thousands of years to crack?
Why Shor’s Algorithm Matters
RSA, or Rivest-Shamir-Adleman, is an asymmetric encryption algorithm and a standard cryptographic technique to encrypt data on the Internet. It uses two different keys: public for encryption and private for decryption.
RSA users can create and publish a public key based on the multiplication of two large prime numbers. And anyone can use this key, since it is open, to encrypt a message. However, the prime numbers must remain secret. Otherwise, anyone can decode the information.
That’s because the prime numbers can be used as a private key to decrypt the message.
Current computers will need many years to break a 2048-bit key. If you use a 1024-bit key, anyone with a sizeable budget backing can crack it within a year. And that is where Shor’s algorithm enters the equation.
American mathematician Peter Shor offered a quantum computer algorithm for integer factorization back in 1994. It solves the following problem that concerns cryptography: Find the prime factors of any given integer.
A capable quantum computer can, in theory, crack all our current encrypted communications in no time using Shor’s algorithm.
But we are still a long way from witnessing such a computer in action. It appears that “Sycamore” demonstrates quantum supremacy within a narrow sampling task. Putting Shor’s algorithm to work requires much more.
Quantum Supremacy – Parting Words
Quantum computing is a viable technology. However, we are not yet sure whether it can do something that a conventional processor cannot.
Furthermore, quantum computers are unstable, which hinders your ability to use them for practical purposes as of today. They also need to store data for long periods to process it faster than conventional machines. But the process consumes lots of energy, which changes the state of qubits, leading to the destruction of saved information.
Everything having the word “quantum” in its name is much more complicated than it appears if you read about it in popular magazines. What it means for your cybersecurity is that current encryption methods are quite safe; for now.
Do you think scientists are on the verge of reaching quantum supremacy? Or do you believe that we are still a long way to go? Tell us what you think in the comment section below.



