SoSafe – Encrypted Chat App with an Embedded GravityRAT Spyware


Android users don’t seem to get a break as they’re always targeted with malicious attacks. A couple of weeks ago, MasterFred invaded the Android systems posing as huge platforms such as Netflix, Instagram, and Twitter.
Now, attackers have found a new way to inject spyware under the guise of an end-to-end encrypted chat application called SoSafe Chat.
GravityRAT is resurfacing again, and we’re here to shed more light on the matter in this comprehensive article.
GravityRAT – The Rat in the Chat
Android has a reputation for being very vulnerable, which makes it an easy target for hackers and the likes.
RAT stands for “Remote Access Trojan,” and the GravittRat is not new to the scene. In fact, back in 2015, a campaign targeted Windows operating systems.
After that, the situation changed and the attackers added Android devices to the mix. In 2020, GravityRat targeted people via an Android app named ‘Travel Mate Pro.” As the name suggests, it’s an app suitable for those traveling.
However, since the pandemic has slowed down traveling, Travel Mate Pro was not cutting it anymore, so the actors moved to a new guise.
This time around, the GravityRat malware took on the form of SoSafe Chat – an app that’s supposed to provide end-to-end encrypted chat services.
According to Cyble, users can download the app through its website. Google Play Store does not have it and has never provided it in the past.
But the question is: How do they get users to visit the page if it’s the only way to download the app? Easy, they use malvertising, social media posts, and instant messages.
What Happens in the Background?
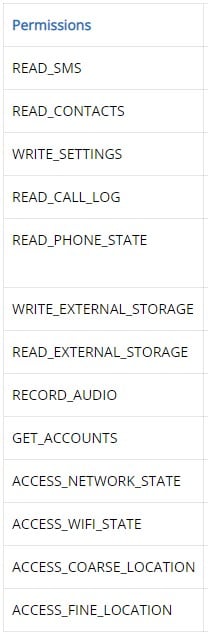
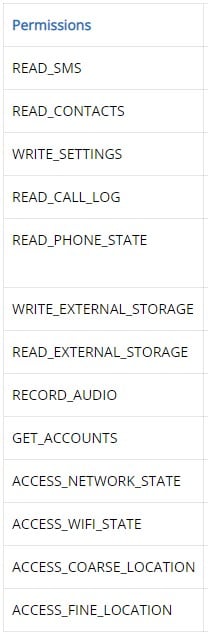
We all have chat apps, so we know what permissions are asked. We’re talking about an extensive list of the following:
Unfortunately, despite not being new, attackers have found new ways to upgrade the malware. Back in 2020, the damage done was big.
However, attackers upgraded GravityRAT to be able to record audio, fetch the device’s location, and exfiltrate cellular network data.
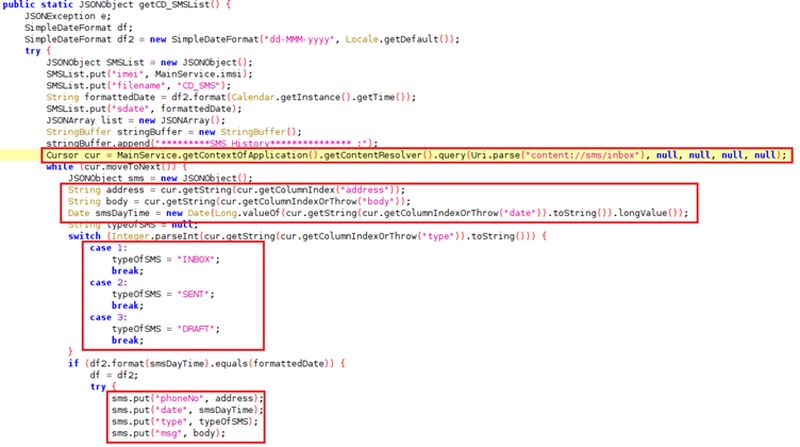
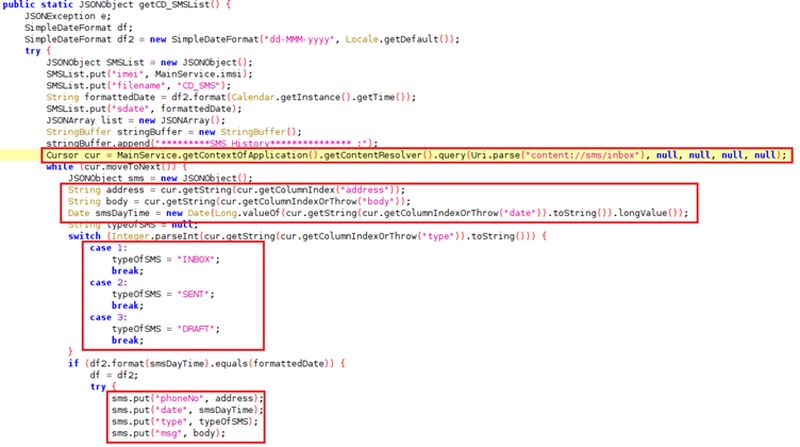
We’ve mentioned a couple of things this malware will be able to do once it sets root. However, there’s a lot more. The spyware can perform a wide range of malicious behavior, including everything on the list below:
- Access SMS, call logs, and contacts.
- Alter system settings.
- Get your phone number and the serial number of your device.
- Record audio.
- Acquire your connection network’s information.
- Pinpoint the exact location of your device.
- Access all the accounts registered to the device.
The previous version of the malware did not have the ability to infiltrate mobile devices. Now, since it can, we have to expect the worse as it indicates that the attackers are actively developing it.
GravityRAT – Dragging Android Users Down
Cyber threats are everywhere and you should be aware of what’s going on. Always double-check the app you’re downloading to avoid such predicaments.
In this case, never download an app from an unofficial source. Even official stores are having trouble keeping up with malware-infected apps, let alone a website you know nothing about.



