Instagram Phishing Attack – Microsoft Email Security Rendered Useless


Phishing campaigns have been spreading all over the world, and fast. However, with time, people who use email adapted and became familiar with how to spot fraudulent messages. This forced cybercriminals to come up with different creative tactics to fool their victims. Yeah, that’s definitely the case with this new Instagram phishing attack.
Apparently, threat actors have been impersonating the social media giant to target students at national educational institutions in the US.
Just like any typical phishing attack, the end goal is to exfiltrate sensitive user credentials. But how are they doing it? How many students were affected? Find out in this article.
We Are Instagram… Not Really!
When it comes to Instagram, this is not the first time it has been used to trick users. A while ago, threat actors started sending emails, promising to award their victims with a “Verified” badge“ next to their profile on Instagram.
That, of course, was all a fluke to lure them in and steal their credentials. Another incident included malicious applications disguised as Instagram and Netflix to spread the MasterFred malware.
Now, Instagram is once again in the spotlight as cybercriminals are using the platform to target yet another wave of victims consisting of 22,000 students at national educational institutions.
It Wasn’t Me – Urgency is Key
Creating a sense of urgency has become a common tactic among threat actors to ensure higher success rates. In this campaign, they’re preying on the victims’ “fear” factor by sending emails warning them of an unusual login.
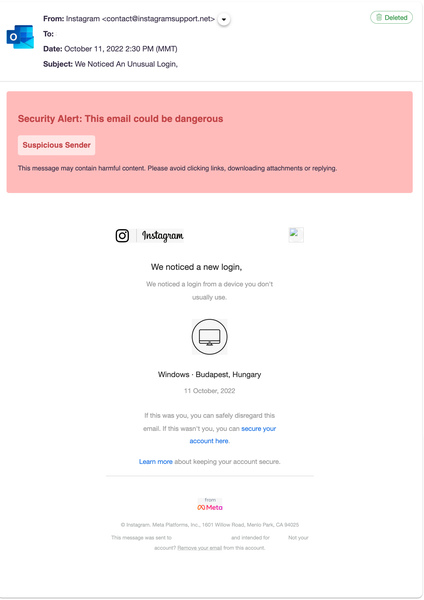
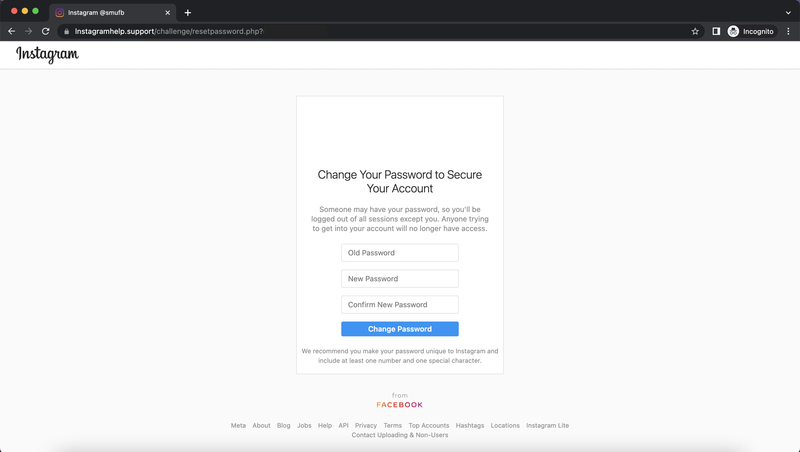
As seen in the image above, immediate action is required. To make this scam more believable, the email shows to be coming from Instagram support with the email [email protected]. Talk about masquerading at its best!
Just like most phishing emails, the victims are prompted to click on a provided link that’ll redirect them to a fake landing page. And we all know what happens there.
In this particular campaign, the provided information leads the victims to click the main call-to-action (secure your account) at the bottom of the email.
Once they click on it, they’ll be taken to the phishing page that perfectly mimics that of Instagram. The fake landing page shows details such as the location where the sign-in occurred. Again, sense of legitimacy.
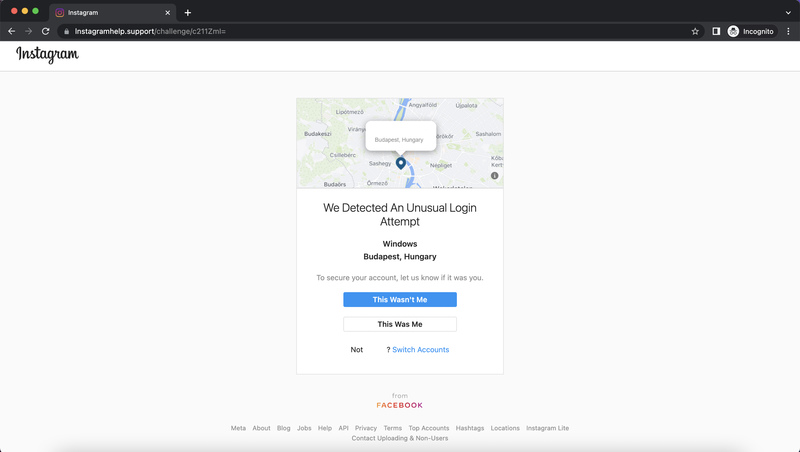
Now, the user has no other option than to click the call-to-action button, This Wasn’t Me. Well, it’s definitely you who they’re after and the second fake page is where they get you.
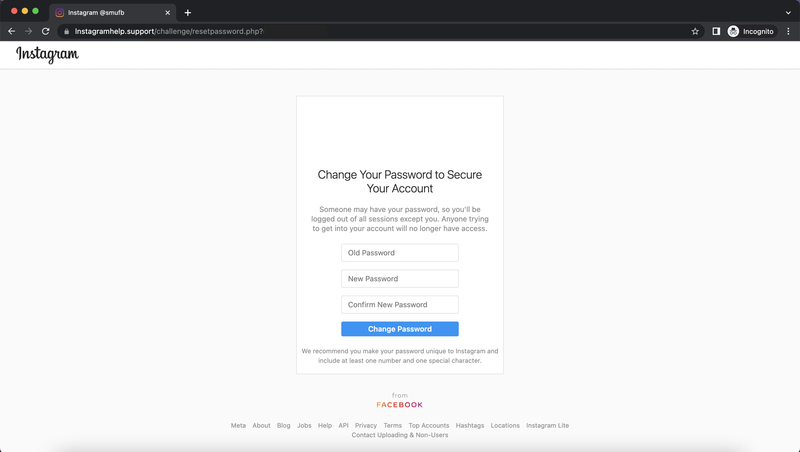
Here’s where the victims should submit their credentials to change their password. We all know what happens here – the landing page’s main goal is to exfiltrate these sensitive user credentials.
Instagram Phishing Attack – Impersonate to Infiltrate
Social engineering isn’t an easy practice, but apparently, cybercriminals are perfecting it. This is one of many phishing attempts using social media platforms as a disguise.
Unfortunately, despite several attacks occurring, victims are still falling for the scams. Whenever you receive an email with a URL, make sure to visit the official source manually. You never know what’s waiting on the other end.



