Itaú Unibanco Trojan: Fake Google Play Page, Very Real Malware Infection


Android devices allow users to download content from all types of sources, which is why they’ve become constant targets for threat actors lately.
Cybercriminals are exploiting that feature to harm users through various activities such as performing fraudulent financial transactions.
Whether it’s from an unofficial source or Google Play Store itself, hackers will find a way to take control of your device.
Unfortunately, the Trojan attack involves none other than Itaú Unibanco – a large financial services provider in Brazil. Yeah, this is another Brazilian bank attack.
With over 55 million customers globally, we can tell how big this attack is. But how are they applying such malware? Find out in the following article.
Another Brazilian Bank Attack – Enter the Trojan
As mentioned, a malicious application is targetting a major banking company in Brazil known as Itaú Unibanco.
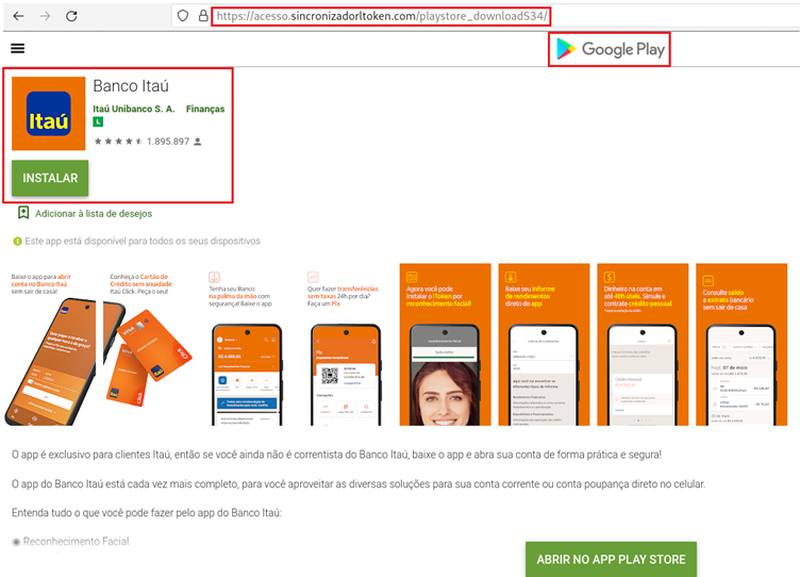
According to Cyble, the threat actors have crafted a fake Google Play Store page from which targets can download the application.
The app itself has a similar icon and name that can easily trick users into thinking it is a legitimate app related to Itaú Unibanco. You can see the fake page in the image below:
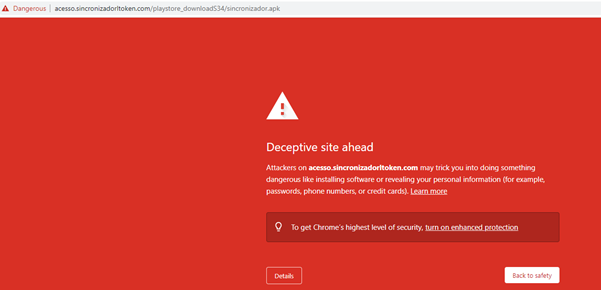
But before the users can get to the download page, the browser they’re using indicates that the URL is “deceptive.” This is exactly what happens when a website is considered to be dangerous to visit.
Now, once the users click on the install button, the page prompts the user to download an APK that goes by the name of “sincronizador.”
This is the new malware that hackers host on the URL: hxxps://acesso.sincronizadorltoken[.]com/playstore_downloadS34/sincronizador.apk.
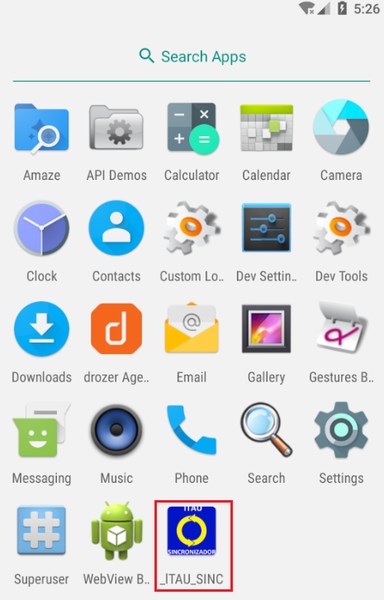
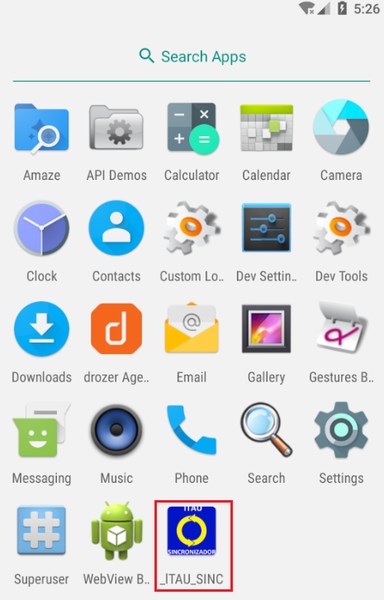
Of course, if the users have the necessary technical background, they’d know that Google Play would never ask them to download APKs. Once the victim downloads the app, it’ll take on the following icon on the device:
The app doesn’t operate by itself. Instead, it uses the actual app to perform fraudulent transactions by manipulating the user’s input fields.
However, before it does that, it has some dangerous permissions to ask for. Why would a banking app ask to observe actions, retrieve window content, and perform gestures?
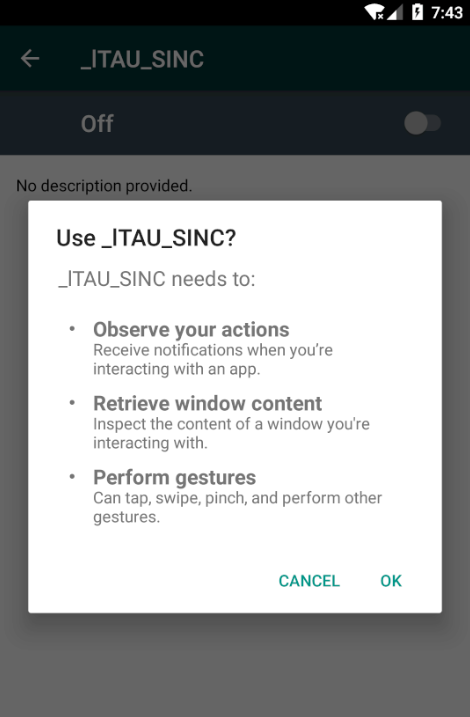
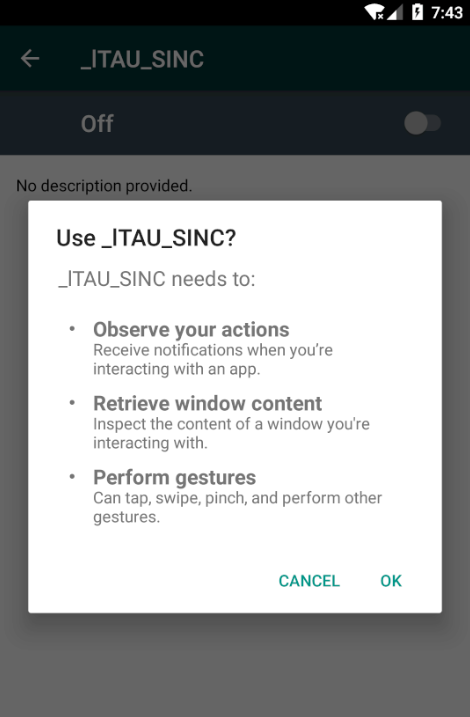
If the users accept the permissions, they’re literally giving the threat actors everything they’re looking for. The _lTAU_SINC/sincronizador Android malware poses a huge threat to everyone.
According to the download page, more than 1.5 million users have installed the app, which is a pretty concerning matter. Cyble reported the malware a while ago. Who knows how many victims this malware has gotten to since.
Itaú Unibanco Trojan – Fake Page with Real Consequences
E-banking offers convenience, but at the same time, it poses a threat if mishandled. To ensure your safety, there are a couple of things you should do.
First, always install the app from the bank’s official website or the Google Play Store – no APKs. Second, get a reputed anti-virus and internet security software package on your connected device.
Finally, use biometric security features such as fingerprint or facial recognition. Please note that you should always keep an eye on the alerts provided by anti-viruses and your data usage.
There might be something off, which indicates that malware is currently present on your operating system. Stay Safe.



