Cynos Malware Alert! 190+ Huawei Apps Infected


Malware campaigns on Android devices have become very popular in recent months. Not long ago, BrazKing hit hard in the Brazilian district, gaining access to bank accounts while masquerading as an Android APK.
And now, a large-scale campaign targeted Huawei’s AppGallery, resulting in approximately 9,300,000 installs of Android trojans disguised as over 190 different apps.
The malware goes by the name of Android.Cynos.7.origin – a platform that has been known since at least 2014, but with some modifications. So, what is this campaign targeting? What intentions could be behind it? Find out in this article.
Enter Cynos – Monetization at its Best
Apparently, the main functionality of this malware version is to harvest information about users and display ads on their devices. Dr. Web stated the following about how this malware operates:
“The Android.Cynos.7.origin is one of the modifications of the Cynos program module. This module can be integrated into Android apps to monetize them. This platform has been known since at least 2014.”
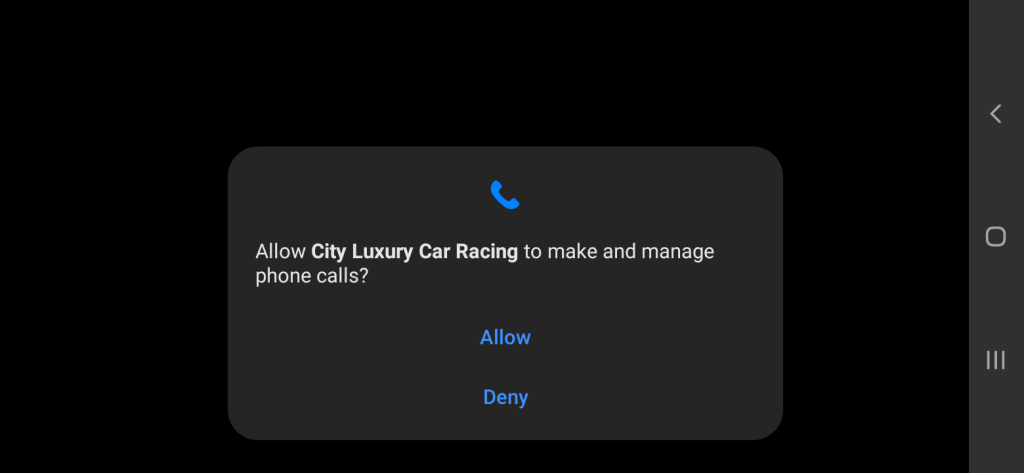
Users with a keen eye for technology would notice that the permissions to perform activities do not generally associate with a game.
Why would a game ask for permission to make phone calls or detect the user’s location if it has no GPS function within it?
According to Dr. Web, once the user grants permission to the app, it starts its malicious activities, collects the following information, and sends it to a remote server:
- User mobile phone number
- Device location based on GPS coordinates or the mobile network and Wi-Fi access point data (when the application has permission to access location).
- Various mobile network parameters, such as the network code and mobile country code; also, GSM cell ID and international GSM location area code (when the application has permission to access location).
- Various technical specs of the device
- Various parameters from the trojanized app’s metadata
Once the attackers collect the data, more malicious magic happens in the background as the malware selects one of the C&C servers listed below and connects to it:
- hxxp://dns1[.]sdkbalance[.]com
- hxxp://dns2[.]sdkbalance[.]com
- hxxp://dns3[.]sdkbalance[.]com
After that, the module receives a server address to send the collected data to and gain all the means to display ads on the victim’s device.
The Not-So-Fun Games
As mentioned, the Trojan was found in more than 190 games on AppGallery, which belong to categories like platformers, strategies, shooters, arcades, as well as simulators.
Unfortunately, the number of downloads is very high as more than 9 million users have gotten the games (Based on the number of installations provided on AppGallery).
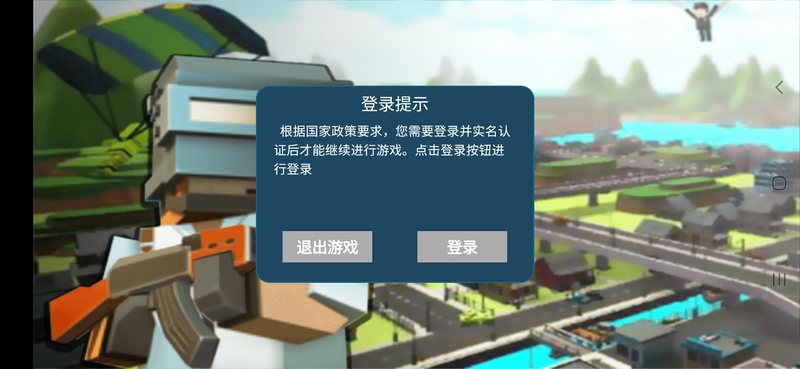
As pointed out by Dr. Web, most of the applications have specific targets such as Russian-speaking users, Chinese individuals, and international audiences.
Below, you can find a list of the top games downloaded from AppGallery with images of how they look like when launched:
- Команда должна убить боеголовку (8000 downloads).


- Cat Adventure (427.000 downloads).


- Drive School Simulator (142,000 downloads).


- 快点躲起来 (2 million downloads)

Unfortunately, it doesn’t stop here. We weren’t kidding when we said that there are more than 190 applications out there containing this Cynos malware. It’s a big list so it won’t fit, but we’ve managed to round up about 15 of them:
- Ace of Sky Hero
- Airplane Master
- Doomsday Sniper
- Battlefield Assault Team
- Bumper Car Arena
- City Mad Drift
- Cliff Diving
- Dino Island Survival
- Escape Terror Nun
- Firefighter Simulator
- Gangster Evil City
- Gunfight Elite
- Millionaire Simulator
- Soldiers United Battle
- Swat War Conflict
The full list is provided by Dr. Web, we just shed more light on some of them in the one above.
Cynos – New Module, Same Devastating Effects
The Cynos malware has been around for over 7 years and different versions have been implemented on millions of devices around the world.
Some of its versions have more aggressive effects such as sending premium SMS, downloading extra modules, and more.
AppGallery has since removed the apps. Now, the users who downloaded them should uninstall them manually. If not, they could inflict more damage than what’s already been done.
Unfortunately, giving advice on how to pick your apps can be tricky here as they were featured on an Official App Store.
But still, make sure you read all the reviews, check as many security websites, such as Anonymania, in order to keep up with what’s going on in the online world.



