Play Store… Again? A New Road to Maliciousness


It hasn’t been long since Google Play Store was distributing malicious applications within its library. In fact, 2 weeks ago, the Android store hosted adware-infected apps with over 20 million downloads. Now, cybercriminals found a new way to practice their activities – redirecting victims to malicious websites.
Apparently, 4 applications made their way to Google Play and have harnessed over a million installations. With such a number, anyone can predict how impactful this campaign is.
So far, researchers are stating that this is part of the adware and information-stealing campaign that hit the Store a couple of weeks ago. What’s it about and what is it after? Find out in the following article.
4 Malicious Apps – 1 Million Installations
As we mentioned, Google Play Store has not been at its best throughout 2022. The application hub has had it rough due to multiple attempts by cybercriminals to infiltrate it.
Despite its various efforts to fend off such attacks, the threat actors have always managed to find new ways to complete their malicious practices.
Whether it’s adware embedded within apps or those that have a postponed action, Google Play does not seem to be keeping up.
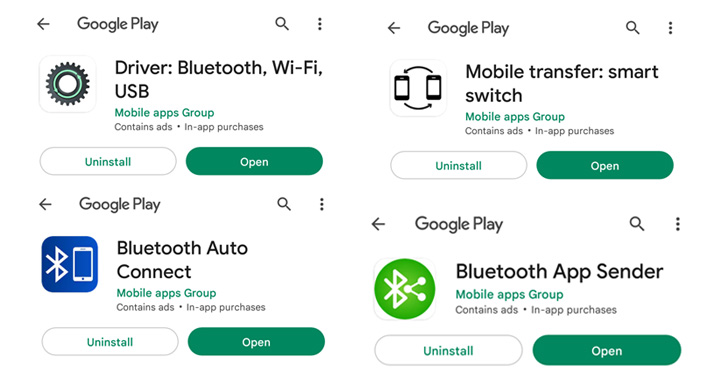
Recently, the app store was also seen hosting applications with 10 million downloads that distributed adware. And now, probably within the same campaign, 4 applications have been redirecting users to malicious sites – not immediately. First, these are the apps in question:
- Bluetooth App Sender – 50,000+ downloads
- Bluetooth Auto Connect – 1,000,000+ downloads
- Driver: Bluetooth, Wi-Fi, USB – 10,000+ downloads
- Mobile transfer: smart switch – 1,000+ downloads

The apps have a delayed action – that’s how they managed to get past Google Play Store’s security measures. This is one of the most popular tactics adopted by threat actors – it introduced time-based delays to conceal their malicious behavior.
According to Malwarebytes, the applications take their time to start their actual practices – approximately a four-day waiting period.
Once this time has passed, they open the first phishing site using the Chrome browser followed by several tabs within a two-hour interval.
So the question is: Does this attack stand on its own or is it part of a much bigger campaign? The second one is your answer as it reflects the HiddenApps campaign that’s been active since June 2019.
Another Incident – Where is this Going?
The incidents with Google Play Store are getting out of hand. The Android store should start elevating its security measures in order to keep up with what cybercriminals are up to.
It can’t rely on the ones it’s implementing now as, apparently, they’re not enough. Threat actors are always finding new ways to bypass them, and they’re succeeding.



