Another Slip Up – Google Play Store Found Hosting Adware
Once again, Google Play Store was found hosting malicious applications. This is probably the 4th incident of the sort in the past 2 months, which makes us question our downloading options. A couple of weeks ago, Google Play infected apps with 10 million downloads. Now, the number goes down to 7 million installs, and the campaign shifted to adware.
The attackers’ plan is quite simple. They’re using Facebook to aggressively promote the malicious apps, and apparently, they succeeded. With so many installs, who knows what damage they’ve inflicted?
Google Play has slipped up again and this kind of attack can have a huge impact, especially considering how the adware works. Yes, we’re going to discuss everything in the following article.
Fool Me Countless Times – The Constant Play Store Infiltration
We seriously have no idea what’s going on with Google Play Store’s security. When it comes to Android, users have the capability to download stuff from any source they want.
This grants convenience, but unfortunately, it comes at the expense of their online security and privacy. Unofficial sources are the perfect place where hackers and cybercriminals lurk to target victims.
That’s why Google Play Store is the best way to get applications as it’s both trusted and safe. Well, we’re starting to question this statement as well recently.
In around 2 months, Google Play Store has suffered more breaches than we can recall. We have to ask if the security measures it’s implementing are good enough to protect its users.
The newest campaign sees attackers promote applications on Facebook. What makes this completely believable is that the victims can clearly see a Play Store link on Facebook, leaving little margin for doubt.
The adware disguises itself as “Cleaning” applications. While these apps are practically useless, for some reason, they’re very popular among users. Here’s an example of a page dedicated to one of the malicious applications:


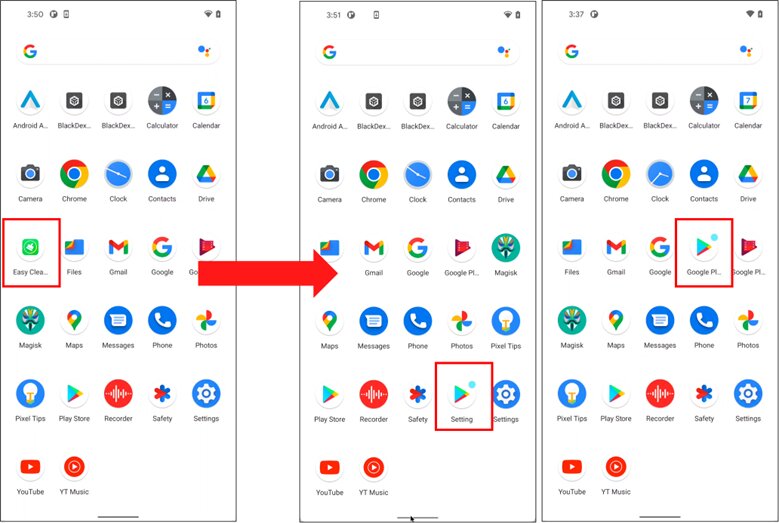
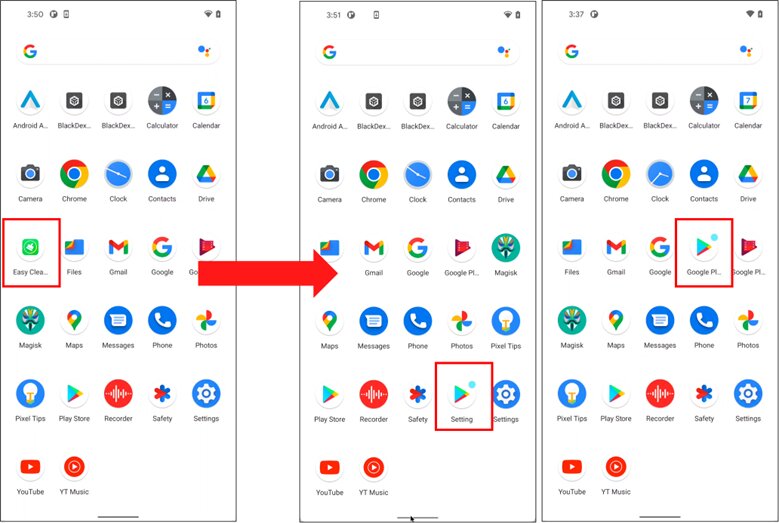
The attack is quite sophisticated and once it sets root, it’s very hard to get rid of. Once installed, the apps will be hard to detect as they’ll constantly change icons and names. They usually disguise themselves as Settings or the Play Store itself.
It’s all in the Contact Provider Android component. According to McAfee, once it’s abused, the apps can then transfer data between the device and online services.
They don’t even have to be launched to perform their malicious practices. The adware initiates itself automatically without any interaction.
A Malicious Clean Sweep
For a better look at what this entire predicament is all about, here are the 12 “Cleaning” apps that have harnessed over 7 million downloads:
- Junk Cleaner – 1M+ downloads
- EasyCleaner – 100K+ downloads
- Power Doctor – 500K+ downloads
- Super Clean – 500K+ downloads
- Full Clean – 1M+ downloads
- Fingertip Cleaner – 500K+ downloads
- Quick Cleaner – 1M+ downloads
- Keep Clean – 1M+ downloads
- Windy Clean – 500K+ downloads
- Carpet Clean – 100K+ downloads
- Cool Clean – 500K+ downloads
- Strong Clean – 500K+ downloads
Apparently and unfortunately, the campaign spread too fast. It started off with countries such as South Korea, Japan, and Brazil, but in the end, it reached a global status in no time.
As of now, all of these applications have been removed from Play Store’s library. Those who still have the apps on their devices should immediately uninstall them.
Yet Another Slip-Up: Google Play Store Adware Detected
The apps must be removed manually from the device. It might be hard due to the constant icon change, but it’s definitely doable.
When you download applications – even from a trusted source such as Google Play Store – always make sure that you give the comments and reviews a quick read.
Check the ratings, and check everything the people say as this may help you avoid a huge predicament in the future.



