Parallax RAT in the Wild – Cryptocurrency Firms Beware!
Injecting Remote Access Trojans on victims’ devices has become a very common practice among cyber criminals. Once it sets the root, it can perform all sorts of commands based on the variant’s functionalities. This time around, threat actors are targeting cryptocurrency companies with the Parallax RAT.
This is not the first time the cryptocurrency industry has been terrorized by cyber criminals. In fact, a while back, the PennyWise info-stealer was used to harvest sensitive browser data and cryptocurrency wallets in a huge campaign.
As mentioned, various variants and functionalities exist. So, what is the Parallax RAT capable of? How much damage can it do? And how is it implemented? We discussed everything below.
Parallax – A Very Risky Crypto RAT
Regardless of whether it’s a company, an individual, or a firm, cybercriminals won’t differentiate the status as long as there are benefits behind it.
We’re referring to financial benefits mostly. The crypto industry has had its fair share of attacks in the past year.
Aside from Pennywise, big companies such as Mailchimp suffered a cybersecurity breach, where hackers gained access to valuable information.
Now, the cryptocurrency industry is under attack by threat actors using the Parallax Remote Access Trojan. This one is quite a handful, as it’s hard to detect due to its ability to hide within legitimate processes. According to Uptycs:
“Once it has been successfully injected, attackers can interact with their victim via Windows Notepad that likely serves as a communication channel.”
The malware can spread across victims via various methods, particularly through spam campaigns or phishing emails (with attachments).
Once it sets root, it can perform all sorts of malicious activities, including complete file access, screen capture, remote desktop control, keylogging, and reading login credentials.
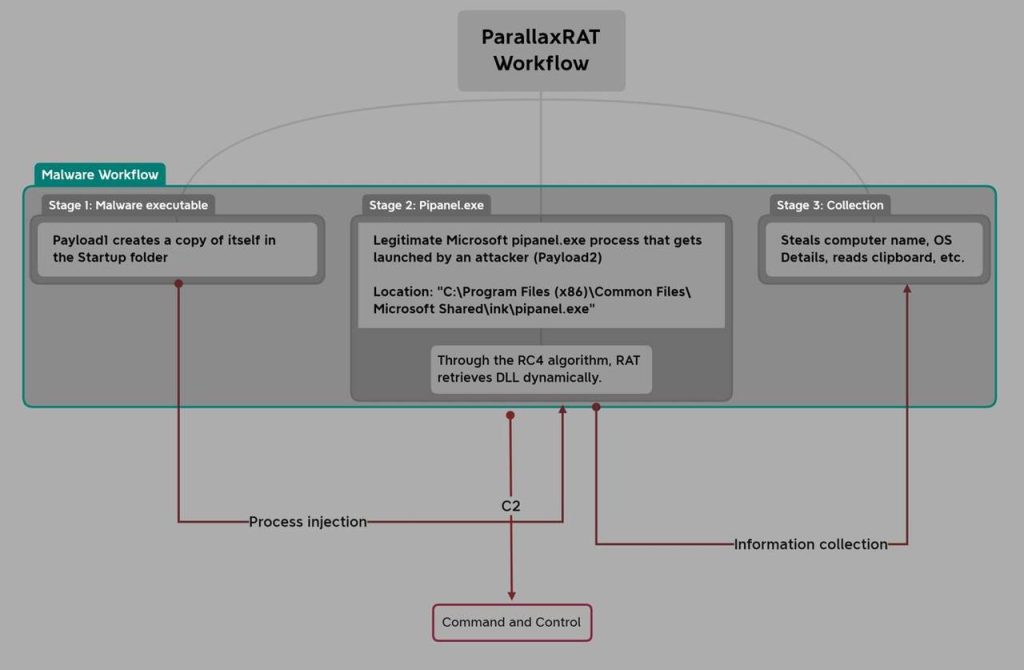
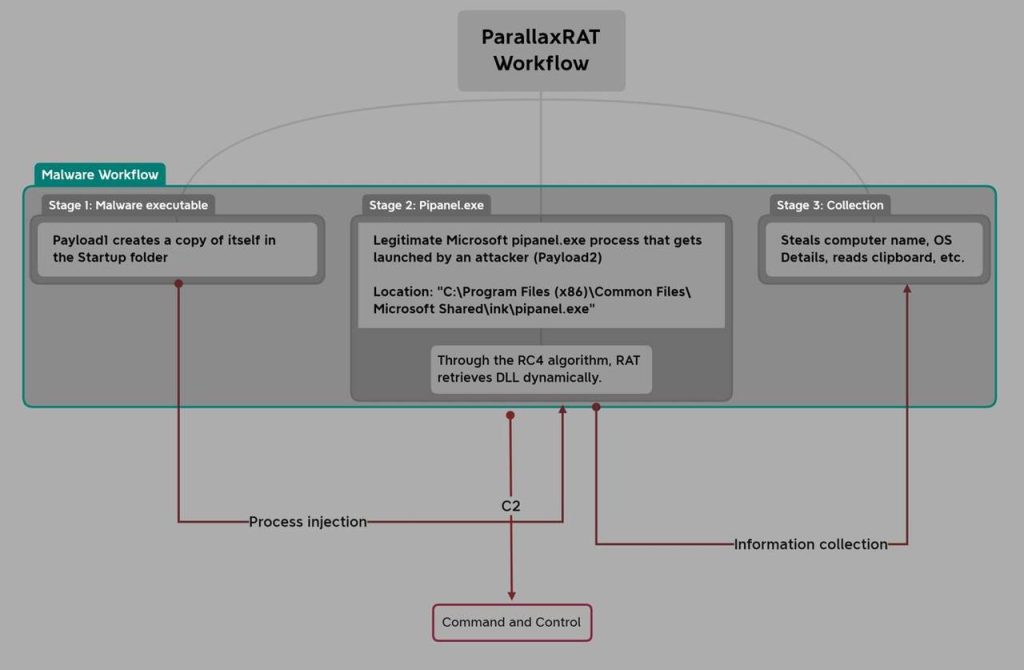
Can you imagine what the threat actor can do with your login credentials? Yes, steal everything you have, especially if you’re signing in to a cryptocurrency application. The following image represents Parallax’s entire workflow process:
But the question is: How and what platform is the threat actor using to target victims? According to the security firm, it’s definitely Telegram, which has recently become a hub for cybercriminals to prey on targets.
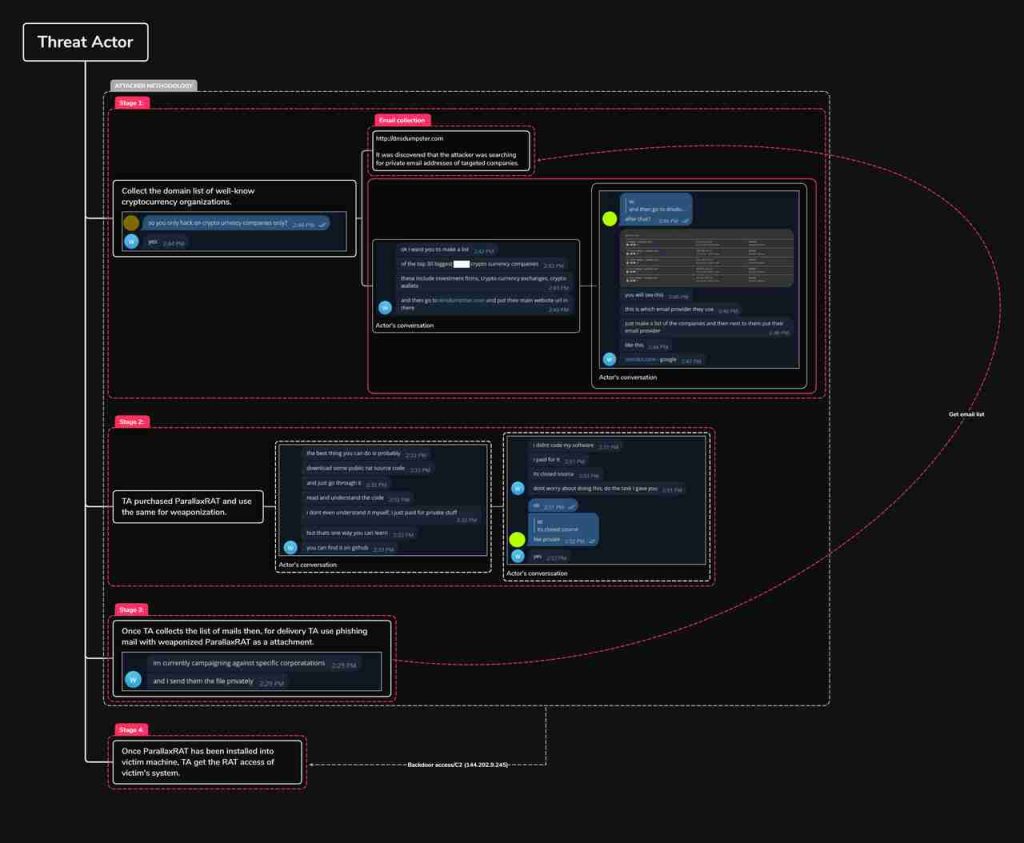
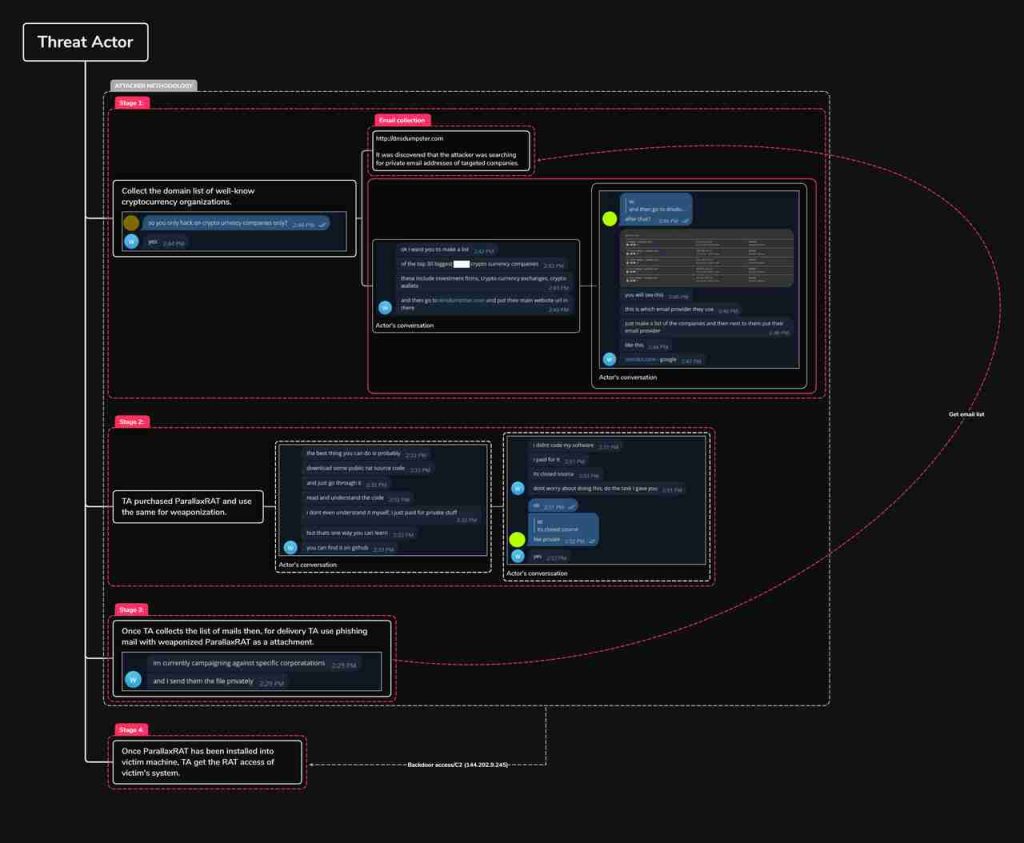
The attackers search for private email addresses of cryptocurrency companies on dnsdumpster.com and then bombard the company with phishing emails. We all know what happens next.
The victim downloads the malicious files, and his/her device gets compromised, allowing Parallax to take over.
There’s A RAT in the Crypto Industry
Uptycs was studying the RAT, and based on their research, they found that a higher number of Parallax RAT samples was spreading recently.
This means one thing only – the threat actors behind this particular campaign are far from done. They will target other companies in the near future, so precautions should be put in place.



