A Sloppy Misconfiguration: Free VPN Exposes Over 1 Million Users


VPNs have become a popular online tool for most internet users. Their sole existence revolves around enhancing online security and privacy.
However, with some providers, that’s not the case. The P in VPN reflects privacy, and a lot of free VPNs don’t seem to get the term.
In fact, recently, QuickFox – a free China-based VPN used by ex-pats and people overseas to access Chinese websites was found leaking unencrypted data of about a million of its users. What happened and who was involved? Find out below.
QuickFox – Seems Foxy, but Very Sloppy
QuickFox is a VPN created by Fuzhou Zixun Network Technology Co., Ltd. The service is mainly used by people living abroad to access Chinese websites such as Mango TV, Tencent Video, IQiyi, and more.
However, there was a shift in this whole process thanks to incomplete ELK stack security. Instead of websites being accessed, the users’ sensitive data was.
According to WizCase, there was a misconfiguration in Quickfox’s ElasticSearch server, leaving it exposed and accessible – with no password–protection or encryption enforced.
The image below shows authentication requests leaking sensitive data:

Let’s explain this a bit more. The flaw was in the ELK (Elasticsearch, Logstash, and Kibana) – three open-source tools that help streamline searches through huge files i.e, a VPN’s logging process.
With such a leak, any person with access to an internet connection and a browser can access these logs and extract personally identifiable information (PII).
As reported by Wizcase, the IP addresses exposed showed that QuickFox users in the US, Kazakhstan, Japan, and Indonesia were mostly affected.
What Was Leaked?
According to Wizcase’s report, 100+ GB of data was leaked, which represents approximately 500 million records.
The leak included two types of data. First, it showed software and applications that are installed on more than 300,000 users’ devices.
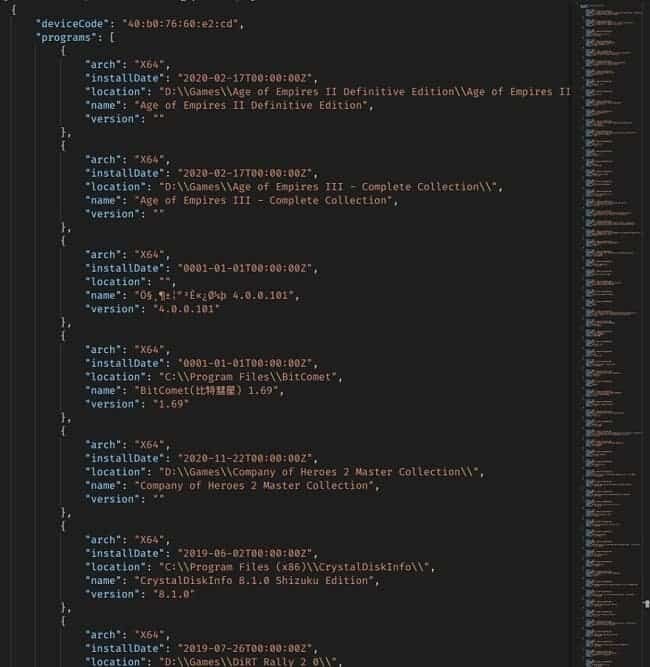
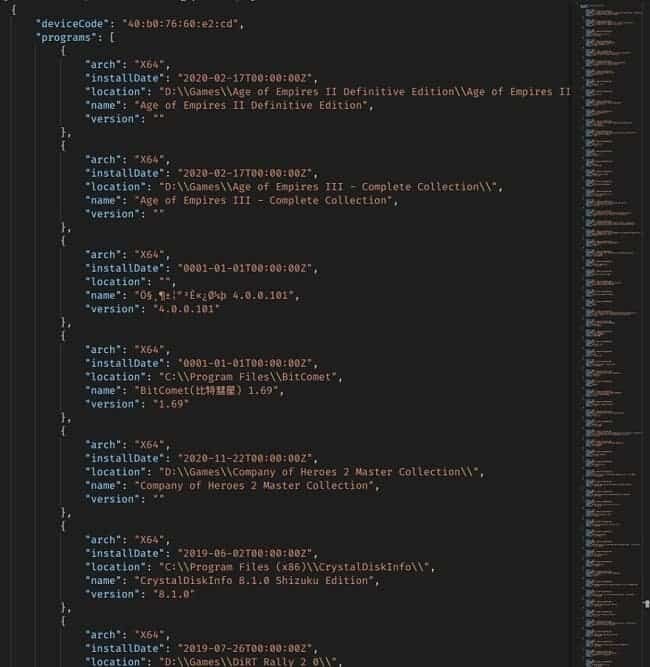
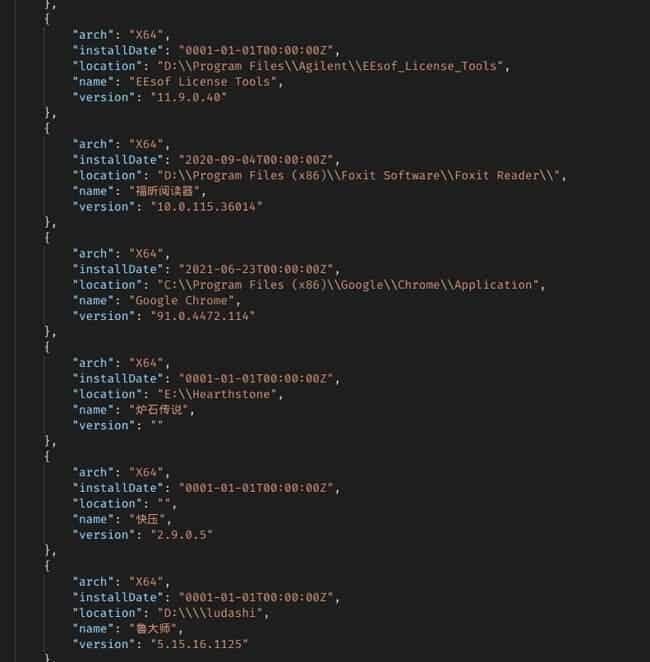
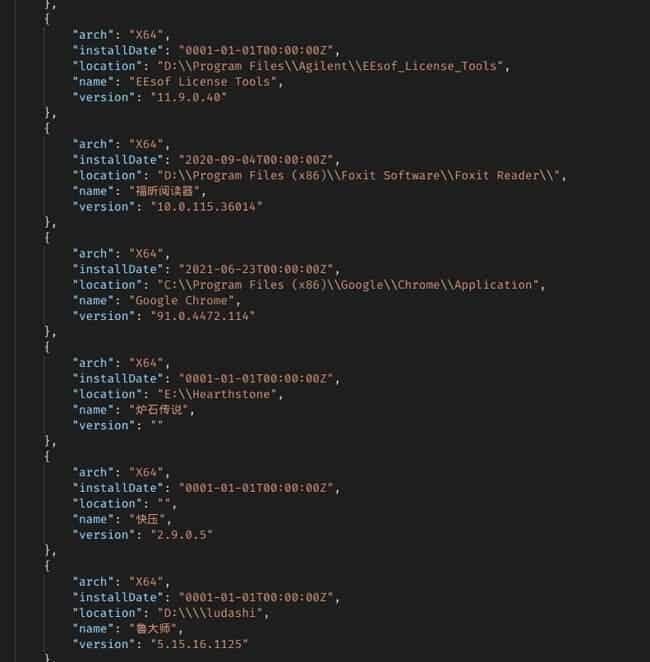
Second, the sensitive and personal information of around 1 million users was exposed to the public. That includes:
- Telephone number (Mobile)
- The users’ real IP address and assigned one.
- Device type information.
- MD5 hashed passwords.
- The locations of their files.
- The software version of the device they’re using.
The worst part is that the leak doesn’t only show the assigned IP address the user got from the VPN, but also the original IP address.
This can lead to drastic repercussions if anyone gets a hold of this information.
QuickFox: Not the Typical Shady Practices
If you don’t know this yet, free VPNs tend to collect some of your data and sell it to third parties.
It’s just the way they operate. How else do you think they keep their service up and running, regardless of the quality.
You become their main source of income. This is common practice among free VPNs.
However, the weird thing here is that the data collected by QuickFox about the software installed on the users’ devices.
We thought that it’s a weird and shady practice, considering this is not the typical method other VPNs use.
Apparently, we’re not the only ones surprised. Wizcase also mentioned this in their statement:
“It’s unclear why VPN collected this data because it’s not needed by the process and isn’t the standard method found in other VPN services. Find Quickfox’s Terms of Service and Privacy Policy and Quickfox extracts it. We couldn’t be sure that the user was aware of the information they were using.“
Why would a VPN collect information that is not even required? Also, why fail to mention any of the collection processes in the Terms of Service?
As of now, there is no official comment from Quickfox regarding this report. Wizcase already did its part in contacting the provider, but they haven’t replied yet.
The China-Based VPN Out-Foxed Its Users
With free VPNs, there’s always a catch. But this time around, there’s a lot more than just collecting user information.
The data collected and leaked may cause serious problems in the future, especially if hackers get a hold of it.
If you’re one of the exposed users, make sure to be vigilant about the potential risks of such a leak as it may result in scams, frauds, phishing attacks, and more.
Most free services need a way to make money, regardless of the consequences. So, when it comes to free VPNs, always do a quick search on the service before using it.



