SpinOK SDK Back Again – One Week, Two Infiltration Attempts


It’s not very common for malware operators to initiate campaigns within a 1-week interval – not with the same malware variant, at least. A week ago, a hundred apps on Google Play with 421 million times ended up hosting SpinOK (Advertisement SDK). Now, 193 new ones have been seen carrying the malicious SDK.
Dr. Web shed more light on the previous incident, indicating the dangers of having this malware lurking around the device. However, the recent incident is being monitored by CloudSEK, which found that the apps have been installed an additional 30 million times.
SpinOK uses minigames that lead to “daily rewards” to spark user interest. This tactic seems to be working based on the number of downloads at hand.
We have to ask: How did it pass Google’s security measures again? What apps are in question? We’ve discussed everything below.
SpinOK SDK Strikes Again – Second Time’s a Charm
When it comes to Android devices, downloading content couldn’t be any easier. Users can simply get their files from any source they stumble upon.
While this provides convenience, it also makes the device susceptible to all sorts of threats across the World Wide Web.
Users might end up on a malicious page that would later deliver malware or some sort of trojan. However, in recent months, threat actors have been utilizing Android’s safest download library – Google Play Store.
Cybercriminals have used Play Store to spread malware several times in the past, and this time it’s no different.
A few weeks back, Dr. Web reported 100+ hundred apps with over 421 million downloads as they were spreading the advertisement SDK, SpinOK. These apps come in the form of mini-games with special rewards – a perfect lure.


The new incident sees 193 apps carrying the malicious SDK. This discovery saw the light thanks to CloudSEK’s security team.
What the users see are harmless mini-games that come with daily rewards. These are actually legitimate and used by the developers to attract more users.
Unfortunately, the malicious activity happens in the background, as SpinOK initiates its actual functionality. Once it’s in place, it’ll harvest files and replace clipboard content.
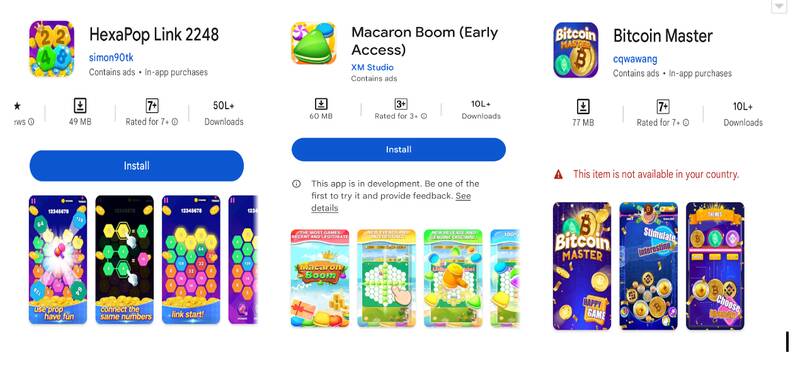
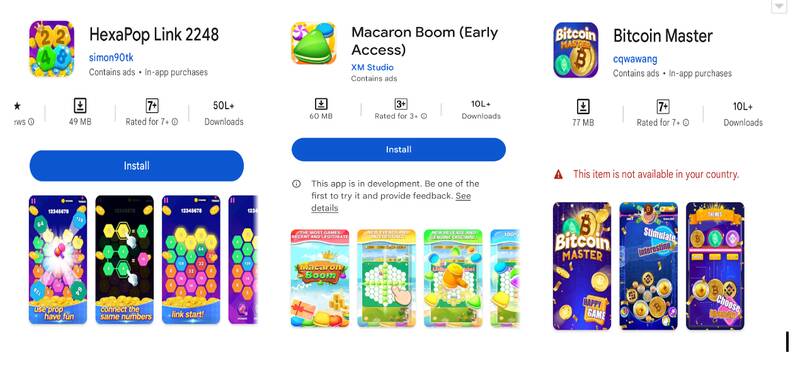
With more than 20 million downloads, this campaign can do a lot of damage. According to the report, the most downloaded of the new batch was HexaPop Link 2248, which had 5 million installations. The rest are as follows:
- Macaron Match (XM Studio) – 1 million downloads
- Macaron Boom (XM Studio) – 1 million downloads
- Jelly Connect (Bling Game) – 1 million downloads
- Tiler Master (Zhinuo Technology) – 1 million downloads
- Crazy Magic Ball (XM Studio) – 1 million downloads
- Happy 2048 (Zhinuo Technology) – 1 million downloads
- Mega Win Slots (Jia22) – 500,000 downloads
CloudSek’s report gives a deeper analysis of the subject at hand, along with a full list of the apps in question.
We have to note that the developers of the app might not have malicious intentions. They just used the SDK thinking it was an advertising library.
Threat actors put these SDKs in the open so that legit developers might stumble upon them and carry out their work for them.
Still There? What Happened?
At the time of writing, CloudSek’s report clearly states that most of the applications are no longer within Google Play’s library.
However, some of them were still there, which begs the question: Why didn’t Google act upon such a discovery and totally eliminate the threat?
Let’s hope Google removes the remaining ones as soon as possible. With the apps’ popularity, the SpinOK SDK can spread very quickly.



