Google Play Store Infiltrated – File Managing Apps with Shady Practices


In the world of cybersecurity, downloading apps from unknown sources could be dangerous. That’s why it’s always recommended to get your content from official stores. In Android’s case, it’s Google Play. However, even the giant can occasionally stumble, which can be seen in a recent incident where the library was found hosting two spyware apps.
Cybercriminals alter their form of attacks every now and then to ensure higher success rates. Masquerading as popular apps can lure a lot of victims… and lure them, they definitely did.
Two file management apps on the Google Play Store were found to be hosting spyware. How does this affect Android users? How do the apps operate once they take root on the device? Who’s behind this campaign? Find out below.
Google Play in the Malicious Spotlight… Again!
Operating an Android device can be very convenient. It allows users to download their content from infinite sources. However, there’s just one that can be described as trusted – Google Play Store.
Yes, convenience doesn’t come without a price, and that’s the device’s security. Infinite sources mean infinite possibilities to get infiltrated, which is exactly what threat actors prey on.
Unfortunately, even the “Trusted” source would sometimes slip and allow cybercriminals to deploy malware-hosting apps within its library.
In fact, Google Play Store has had its fair share of such incidents, with one literally involving applications spreading the SpinOK spyware among users.
Now, two popular applications were found on the Android store with spyware that sends sensitive data to Chinese servers.
File management apps on the Google Play Store are, without a doubt, very popular. That’s why these two applications have harnessed a combined download number of 1.5 million.
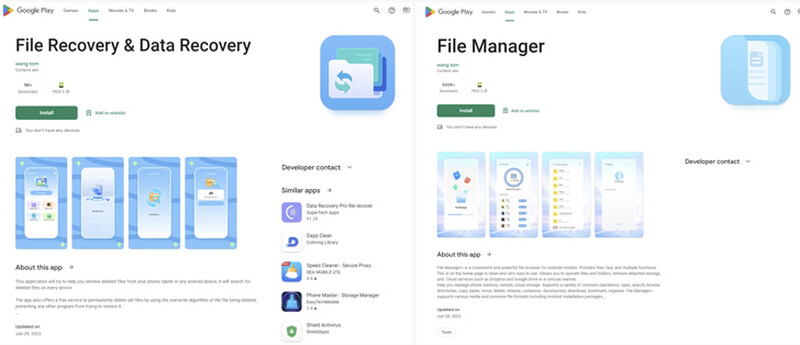
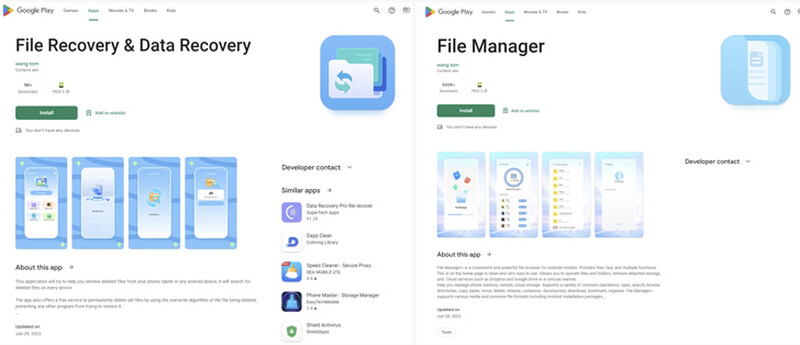
Both “File Recovery & Data Recovery” and “File Manager” apps present users with a lot of promises and features… on the surface.
However, according to Pradeo’s analytics engine, they collect various personal information in the background without users’ knowledge.
When we say various, we mean it. These spyware-injected applications harvest a lot of sensitive information, including:
- Contact lists
- Media files (images, audio, and videos)
- Real-time location
- Mobile country code
- Network provider details
- SIM provider network code
- Operating system version
- Device brand and model
Based on Pradeo’s findings, the process is more alarming than the harvested data listed above. These applications perform more than a hundred transmissions each. Not to mention a huge amount of malicious activities in the background.
When the spyware siphons the information, it sends it straight to several servers in China. It gets worse.
The threat actors behind this campaign used elevated techniques to make the apps appear more legitimate and difficult to uninstall.
Malware and spyware variants are always evolving and finding new ways to infiltrate trusted platforms. Make sure to take proper precautions before you download applications.
Spyware Apps Invade Google Play
When we say that hackers are using elevated techniques, we mean it. Now, they can easily create a false sense of trustworthiness by artificially increasing the number of downloads of apps.
They can simply operate using install Farms or mobile device emulators, tricking users into downloading the apps without thinking twice.
The good news is that Google Play has removed the infected applications from its library. If you downloaded any of these applications, make sure to uninstall them now by any means necessary.
Also, we highly recommend caution when downloading apps. Check the ratings and reviews – a large user base is not enough to deem an app legit.



