A Dangerous Campaign – Chrome Extensions Taking Malicious Routes


In the world of cybersecurity, we’ve seen everything related to hacking and infiltration methods. We’ve seen phishing attacks, smishing, ransomware, as well as app impersonation. The latter is very common among Android users. However, turning Chrome extensions into malicious tools? That’s uncommon, but it’s definitely there, and it’s dangerous.
Chrome extensions are very popular as they tend to ease the users’ browsing experience and add a little convenience to it.
Unfortunately, in a recent campaign, these tools’ popularity was utilized by threat actors, who added 32 malicious extensions to Chrome Web Store.
Collectively, these extensions come with a download count of 75 million, which shows how big and dangerous this attack is. What are the extensions in question? What can they do once installed? Find out below.
Malicious Chrome Extensions – 75 Million Downloads
As we mentioned, Extensions reflect convenience. They give us the option to browse the web and do various things a web browser alone does not offer.
Every now and then, threat actors use popular platforms to spread their malware. For example, Youtube alone has witnessed several incidents where cybercriminals use its videos to promote malicious websites.
Now, this particular campaign is targeting victims through extensions already embedded with malware. One of these extensions is something every Youtube user craves – an Auto Skipper.
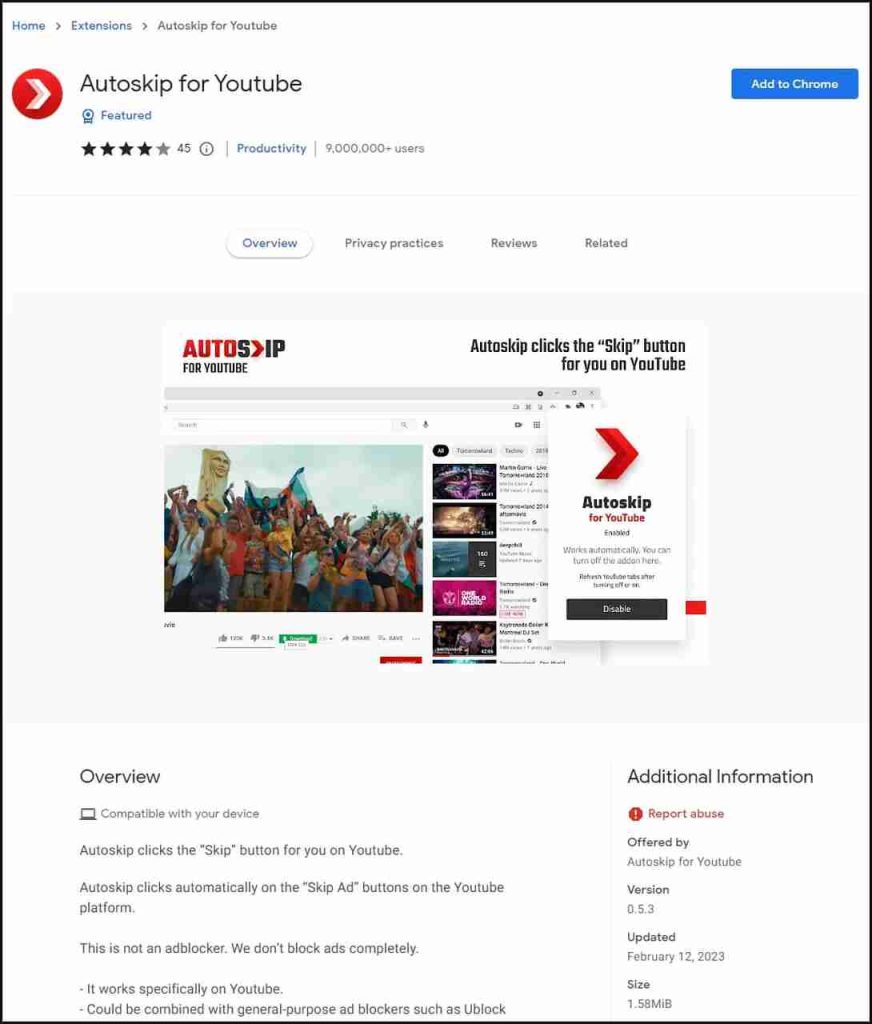
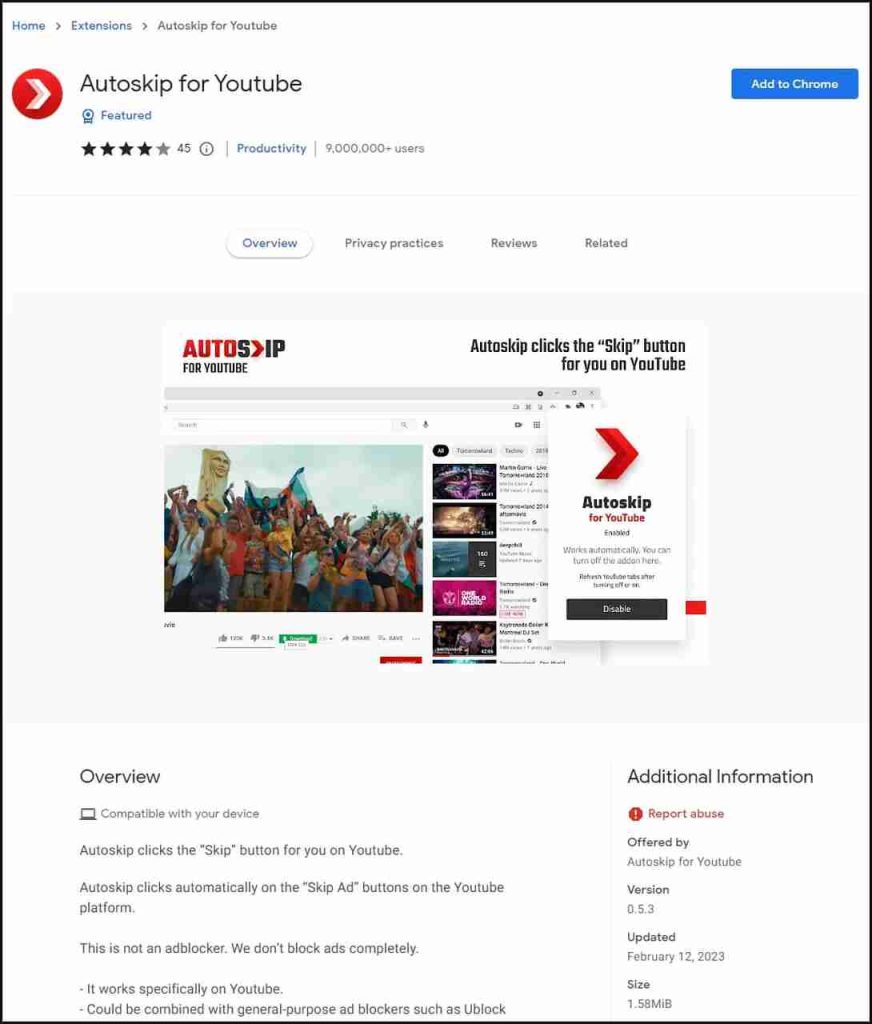
That’s why, it alone, harnessed over 9 million downloads. With such a high number, we can easily tell how dangerous all of this is.
Overall, there are 34 malicious extensions. We’ve listed the top ones based on how many times users have downloaded them: (The Full List)
- Auto skip for Youtube (9,008,298)
- Soundboost (6,925,522)
- Crystal Ad block (6,869,278)
- Brisk VPN (5,595,420)
- Clipboard Helper (3,499,233)
- Maxi Refresher (3,483,639)
- Quick Translation (2,797,773)
- Easyview Reader view (2,786,137)
- PDF toolbox (2,782,790)
- Epsilon Ad blocker (2,571,050)
- Craft Cursors (2,437,224)
- Alfablocker ad blocker (2,430,636)
While assessing one of the infected extensions, researcher Wladimir Palant found code that was disguised as a legitimate extension API wrapper.
According to his report, if threat actors were to abuse it, they could easily insert ads into web pages and steal sensitive information.
Also, while analyzing some of these extensions’ codes, the researcher found out that some of them activate 24 hours after installing the extension.
This type of behavior is usually associated with malicious activities to seal the malware’s presence on a device. Wladimir did report to Google, but they failed to remove the extensions at the time.
When Avast stepped in, Google reported that extensions had been removed from the Chrome Web Store.
Malicious Extensions Begone
Avast, as the huge cybersecurity firm it is, neutralized the malicious elements within the extensions. However, it did let the legitimate features continue operating without disruption.
Now, none of the extensions exist within the Chrome Web Store anymore, but that doesn’t mean no similar attempts won’t pop up in the future!
When you download software or any type of extension, make sure to read the reviews first. Even if it’s from a trusted source, you never know who’s behind them and what their intentions are.



