EyeSpy Surveillanceware: Compromised VPNs Out in the Open
Virtual Private Networks (VPNs) exist solely to elevate a user’s online privacy and security. However, in recent malicious campaigns, these trusted tools have been used in a tainted form to spread the infamous EyeSpy Surveillanceware.
A lot of individuals around the world put their faith in VPNs to secure their data. But with such a campaign taking place, everything is at risk as the malware tends to harvest sensitive information from any infected machine.
Disguising as a VPN is the ultimate way to gain anyone’s trust, and apparently, it’s working perfectly fine. What is this attack all about? How is the malware executed? Find out below.
EyeSpy with My Little Eye… Sensitive Information
The demand for VPN services has seen a huge spike in popularity over the past few years. Aside from enhancing online security, these utilities allow users to anonymize their internet browsing as well as bypass restrictions/censorship.
Unfortunately, popularity grabs threat actors’ attention, and that’s exactly what happened recently. VPNs are an escape from limitation, especially in oppressive countries such as China and Iran. Some are free (Not safe), some are premium, and others are downright laced with malware.
A while ago, one of the biggest names in the VPN industry, ExpressVPN, was impersonated to spread the very dangerous RedLine Malware.
Now, since Iranian residents need VPNs, 20Speed VPN, an Iranian-based service, is being used to spread the malware via trojanized installers.
Once the malware takes root, it can harvest all sorts of information, including:
- Stored passwords
- Crypto-wallet data
- Documents and images
- Contents from clipboard
Aside from that, EyeSpy can take full control over the infected device. Yes, it can easily lead to identity theft and financial loss, as it can also take screenshots, record microphones, and log keystrokes.
The Infection Process
According to a study by Bitdefender, here’s how the entire process goes like this:
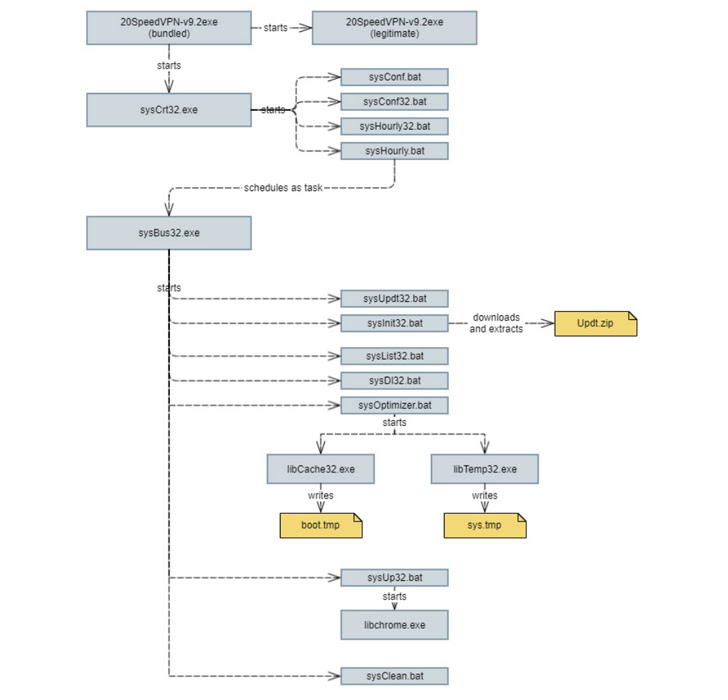
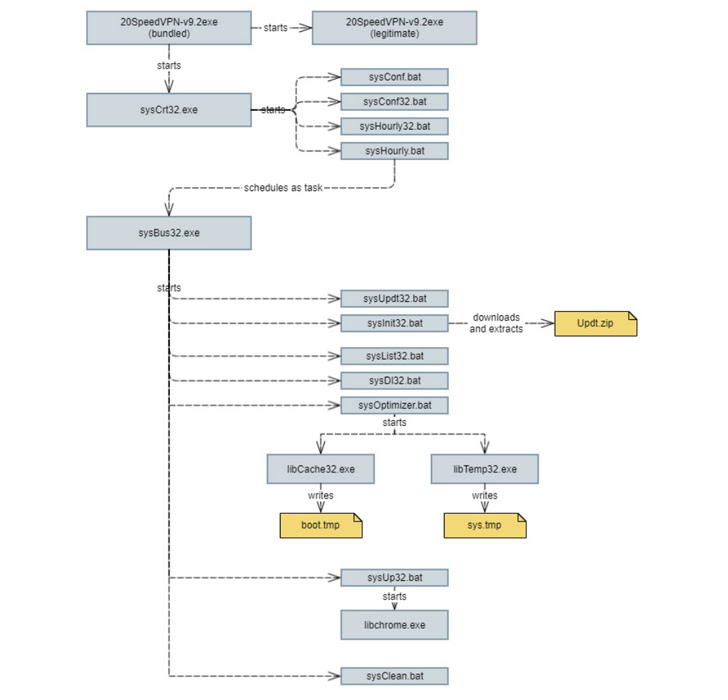
It all starts with a legit installer downloaded straight from 20Speed VPN’s website. Yes, this gives us an idea of what’s been going on – the website might have been breached. We’re not rolling out the idea that Iran deliberately wants to spy on its residents (That’s another scenario to consider).
When the users install the app, the legitimate version will take root on the device. However, it stealthily kicks off a chain of activities in the background in which it installs further payloads to harvest personal information from the infected host.
20Speed VPN is a paid service, but just like most VPNs, the installer can be downloaded from the website without making any prior payments. In other words, users will install the spyware components anyway.
20Speed VPN – A Virtual Spyware Network
According to the study by BitDefender, EyeSpy is capable of various intrusive practices, including fully compromising online privacy via keylogging and stealing sensitive information.
VPNs are supposed to be a way to avoid censorship and bypass online restrictions. However, some governments may tag along to solidify their presence and monitor everything their residents do online.
If you’re looking for a paid VPN service, it’s highly recommended you stick to top names and brands in the industry. It’s worth the time, as your private information is at stake here.



